13 Best GRC Software Solutions by Category
.png)
GRC software sits at the center of how organizations manage governance, compliance, and risk. It brings structure to processes that would otherwise be scattered across spreadsheets, emails, and disconnected tools, centralizing policies, controls, audits, and vendor records into a single system of record. For teams dealing with frequent audits and shifting regulatory requirements, that level of organization is critical.
But the context around GRC has changed. According to Verizon’s 2025 DBIR, 30% of breaches now involve a third party (double the previous year), driven by increased exploitation of vulnerabilities and operational dependencies. Risk is no longer confined to internal controls or periodic reviews. It is distributed across vendors, integrations, and external systems, which shifts what teams need from these platforms.
Understanding these differences and where each platform falls short will help you manage risk consistently and effectively across your organization.
What Are GRC Software Solutions, and How Do They Work?
GRC software solutions are solutions that help organizations manage governance, risk, and compliance activities more systematically. In practical terms, that usually means centralizing policies, controls, assessments, audit evidence, issues, remediation workflows, and reporting so teams don't have to coordinate everything through spreadsheets or disconnected systems.
It’s important to note that GRC software is now an umbrella term covering very different products. Traditional enterprise GRC platforms served as centralized systems of record. Over time, cloud adoption, expanding regulatory requirements, and vendor sprawl pushed the market into more specialized categories, from compliance automation to external security ratings. Each category addresses a different operational need.
Most GRC tools are strong at documenting workflows, helping teams record controls, assign owners, track assessments, and show evidence during audits. That has real value, but the problem is that documenting a risk process is not the same as validating whether risk exists.
Many platforms can tell you whether a vendor completed a questionnaire, submitted a report, or passed a workflow checkpoint, much like a checkbox exercise. Fewer can tell you whether the vendor actually delivers meaningful exposure in your environment; hence, the importance of truly understanding your GRC tool’s capabilities before purchasing it.

Benefits of GRC Software Solutions
GRC platforms provide structure for managing third-party risk throughout the vendor lifecycle. The most meaningful benefits include:
- Centralized vendor inventory and lifecycle tracking: Provide a single source of truth for all third parties, including ownership, risk tier, assessment status, and lifecycle stage, so teams can clearly see who is onboarded, under review, or overdue for reassessment.
- Standardized vendor assessment workflows: Enable you to run questionnaires, evidence collection, and control validation through consistent workflows, reducing back-and-forth with vendors and ensuring assessments are executed the same way across the organization.
- Improved evidence management and audit readiness: Store vendor-submitted documents, certifications, and audit artifacts in a single location, making it easier to demonstrate due diligence and respond to internal or external audits without scrambling for documentation.
- Clear ownership and cross-functional coordination: Align security, procurement, compliance, and legal teams within a shared system, with defined responsibilities and fewer gaps or duplicated efforts during vendor onboarding and reviews.
- Ongoing tracking of reassessments and remediation: Monitor assessment cycles, expiring evidence, and remediation tasks to ensure your team can re-evaluate vendors on time and follow identified issues through to closure.
These benefits are operational, but important. They make vendor risk programs more scalable, reduce manual coordination, and help teams stay on top of growing third-party ecosystems. At the same time, they primarily improve vendor risk process management, not necessarily how vendor risk is understood or validated.
13 Best GRC Software Solutions by Category
How we rated these tools
We chose these tools based on how well they reflect what modern teams actually need from GRC platforms. That includes how deeply they surface risk beyond basic recordkeeping, whether they validate vendor claims or simply collect them, and how effectively they combine external intelligence with internal business context. It also considers whether the platform supports ongoing monitoring rather than point-in-time workflows, and whether it helps teams take meaningful remediation action.
Agentic AI-Native Third-Party Risk Platforms
This is the most advanced category in the market. These platforms combine automation, external intelligence, and internal context to deliver deeper, more continuous visibility into third-party risk.
Key features to look for
- Artifact analysis powered by Agentic AI
- External intelligence and OSINT
- Continuous vendor monitoring
- Context-aware risk prioritization
- Actionable remediation guidance
1. Lema.ai
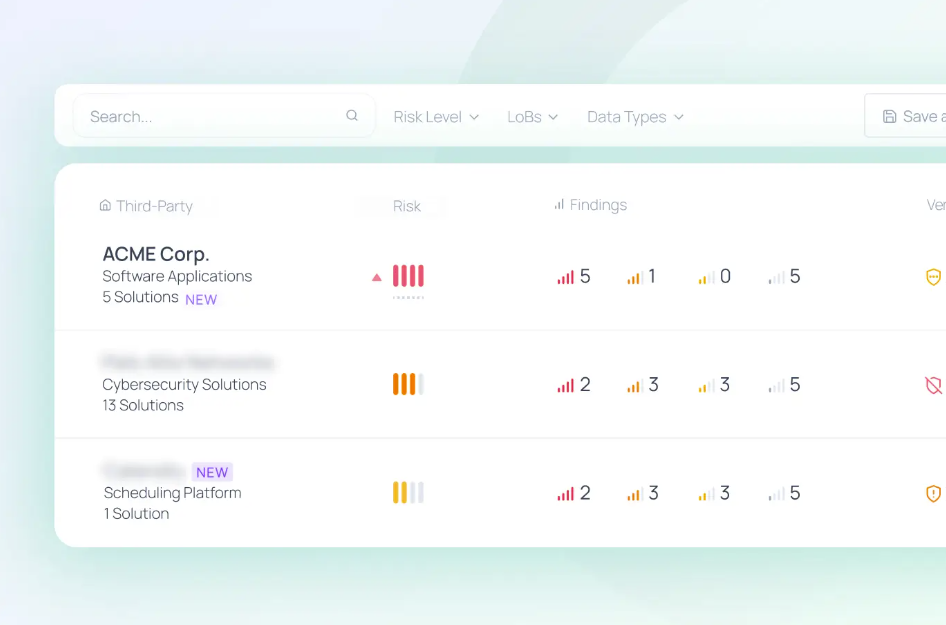
Lema is a Risk Engineering platform rather than a traditional GRC tool. Its differentiation is not just faster workflows. It uses Forensic AI Assessment to analyze vendor artifacts, Open-Source Recon to validate claims against publicly available evidence, and Blast Radius Monitoring to map how a vendor is actually connected to your environment.
Blast radius, in this context, refers to the scope of access, data exposure, operational dependencies, and potential business impact tied to that third party. Lema then correlates those layers through Agentic Risk Engineering to surface evidence-backed findings and concrete remediation steps. These capabilities combined make this platform unusually strong for teams that need to know whether a vendor creates real exposure, not just whether the paperwork looks complete.
Best for: Security-led teams that want to validate and reduce third-party exposure.
When to avoid it: Avoid if your focus is on checking the box and auditing, not looking to actually find vendor risks.
Score: 9.5/10
2. Drata
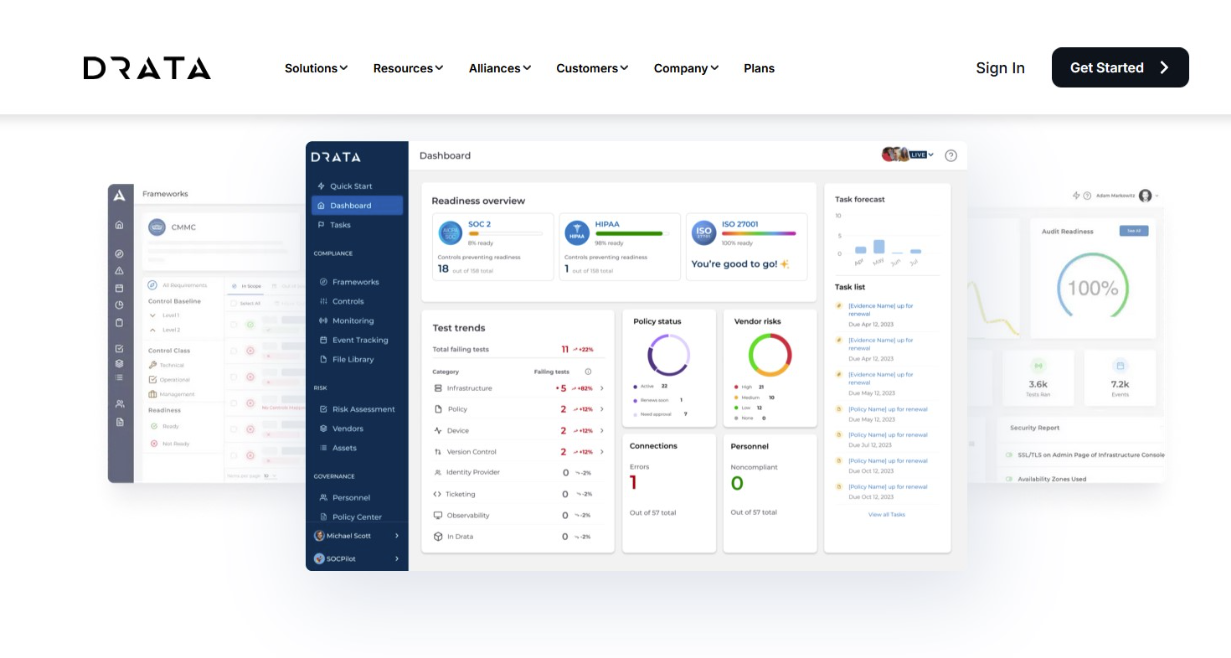
Drata is best known for compliance automation, but it has expanded into adjacent trust and risk workflows. It is strong in continuous monitoring, automated evidence collection, and maintaining audit readiness, which makes it attractive to companies seeking a single platform that spans security compliance and vendor or risk oversight. Its strength lies in operational efficiency and broad trust management coverage, not in forensic validation of third-party risk.
Best for: Companies that want compliance automation first, with broader trust management capabilities.
When to avoid it: Avoid it if third-party exposure analysis is your primary buying driver.
Score: 7.8/10
Compliance Automation Platforms
These tools help organizations achieve and maintain compliance with frameworks such as SOC 2, ISO 27001, and GDPR by automating evidence collection, control mapping, and audit workflows.
Key features to look for
- Automated evidence collection and integrations
- Pre-built compliance frameworks
- Continuous control monitoring
- Audit workflows and reporting
- Policy management
3. Vanta
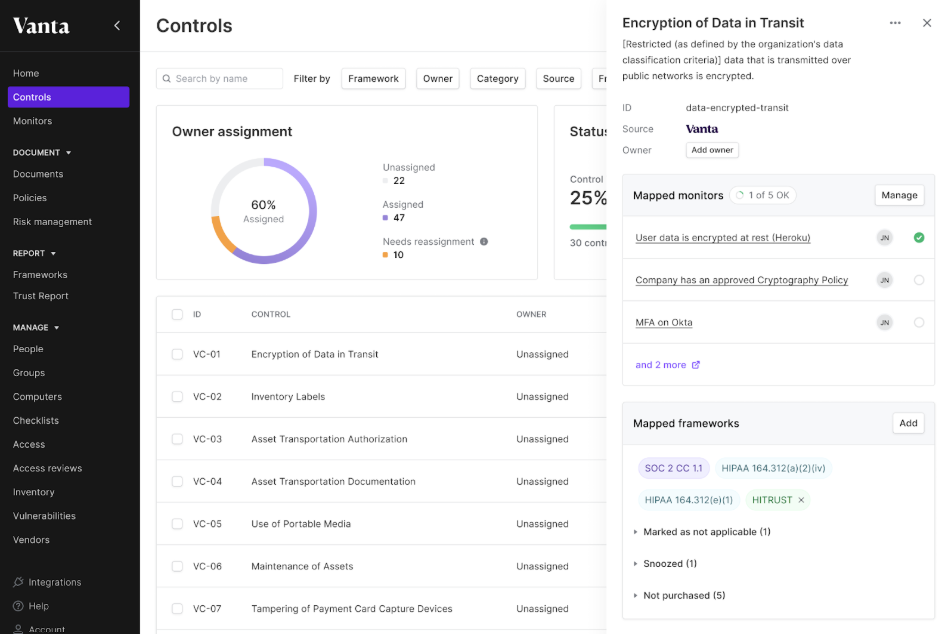
Vanta is one of the most established names in compliance automation. Its core values are automating evidence collection, continuously monitoring controls, and providing teams with a centralized view of policies, issues, risks, and vendor records. It is especially strong for fast-moving companies that want to compress audit prep and reduce manual compliance work. The tradeoff is that its risk capabilities are still mostly oriented around program management rather than deep exposure analysis.
Best for: Organizations prioritizing audit readiness and multi-framework compliance automation.
When to avoid it: Avoid it if you need a highly specialized third-party risk investigation.
Score: 8.4/10
4. Secureframe
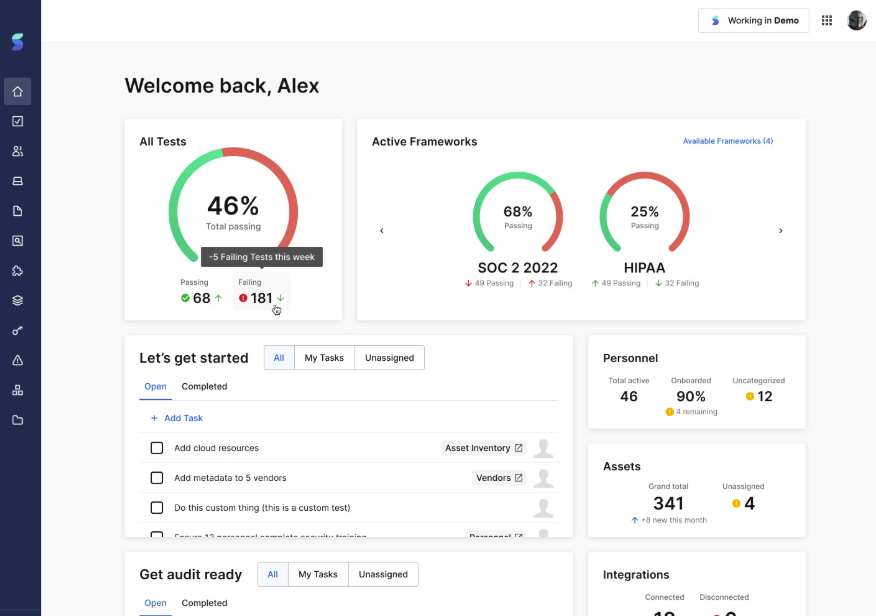
Secureframe is a compliance automation platform that helps teams achieve and maintain frameworks such as SOC 2, ISO 27001, and HIPAA with less manual effort. It automates evidence collection by integrating with cloud infrastructure (e.g., AWS, Okta, GitHub), continuously tests controls against framework requirements, and surfaces gaps with guided remediation steps tied to specific compliance controls.
It continuously tracks control status, flags drift, and maintains audit-ready evidence, reducing the burden on security and GRC teams. However, its model is centered on compliance execution. Vendor risk is assessed through frameworks, attestations, and control coverage.
Best for: Teams that want a structured, automation-heavy path to ongoing compliance.
When to avoid it: Avoid it if you need a platform built primarily around third-party exposure analysis.
Score: 8.1/10
Vendor Risk Management (TPRM) Platforms
These platforms manage the lifecycle of third-party risk through onboarding, due diligence, assessments, ongoing reviews, and reporting. They are usually workflow-heavy by design.
Key features to look for
- Vendor onboarding and intake workflows
- Risk tiering and segmentation
- Questionnaire automation
- Assessment tracking and reporting
- Vendor inventory management
5. OneTrust

OneTrust is a broad governance platform spanning privacy, compliance, and data governance, with third-party risk management as one of its core modules. It helps organizations standardize vendor onboarding, risk tiering, assessments, and monitoring through configurable workflows and a centralized vendor inventory. Its strength is operating at an enterprise scale. OneTrust enables consistent processes across business units and integrates external risk intelligence such as security ratings, breach data, and adverse media, with monitoring driven by these feeds and automated triggers.
Best for: Enterprises that need structured, high-scale third-party workflows across business units.
When to avoid it: Avoid it if you want a more security-native, evidence-led risk model.
Score: 8.0/10
6. ProcessUnity
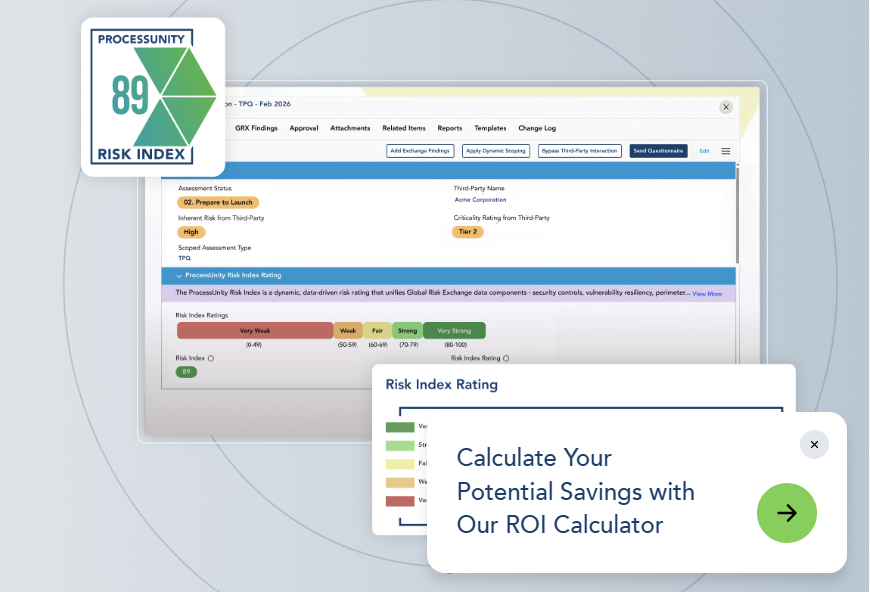
ProcessUnity operationalizes vendor risk programs at scale. It focuses on workflow orchestration across the full vendor lifecycle, including onboarding, risk tiering, due diligence, continuous monitoring, and offboarding. The platform is highly configurable, allowing teams to tailor assessment workflows, automate reviews, and align processes with internal policies and regulatory requirements. ProcessUnity also incorporates AI-driven evidence evaluation to analyze vendor documentation and highlight control gaps. However, its model remains primarily program-driven.
Best for: Mature TPRM programs that need configurable workflows, scalable due diligence, and strong lifecycle management.
When to avoid it: Less suitable for teams looking for investigation-led analysis, deep validation of vendor claims in context, or strong linkage between vendor risk and internal exposure.
Score: 7.7/10
7. Whistic
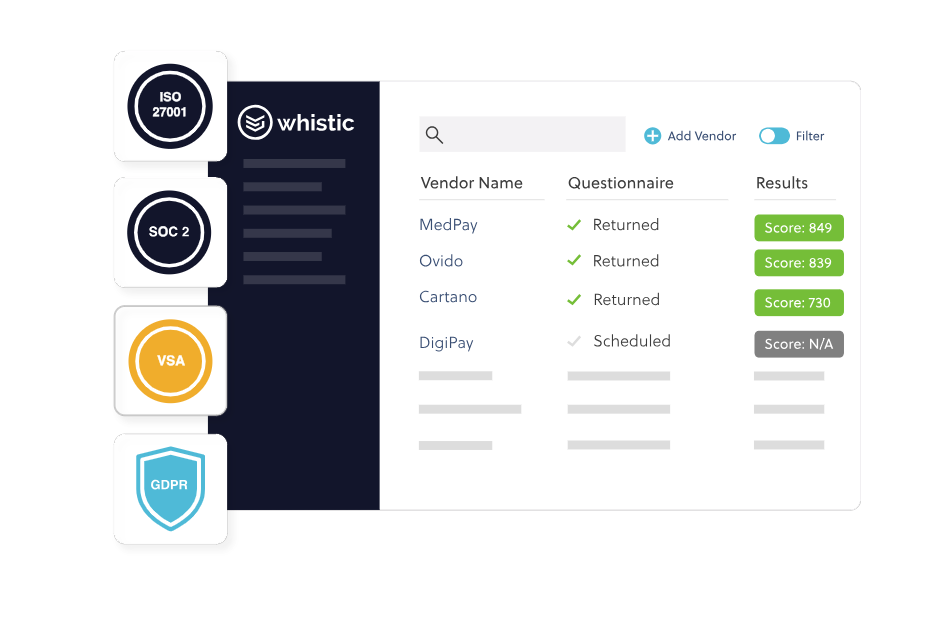
Whistic’s core model centers on the Whistic Trust Exchange, a shared network where vendors can publish completed assessments, security documentation, and trust profiles that can be reused across multiple customer requests. This significantly reduces the need for repetitive questionnaires and back-and-forth during due diligence.
The platform also supports AI-assisted questionnaire completion, evidence management, and basic vendor monitoring through integrations and external data. Its strength is speed and efficiency in the assessment process. However, risk is still primarily understood through shared responses, vendor-provided data, and external signals, rather than deep analysis of each vendor.
Best for: Teams trying to speed up vendor reviews and reduce questionnaire fatigue.
When to avoid it: Avoid it if you need rich internal context mapping or blast-radius analysis.
Score: 7.6/10
8. Mitratech
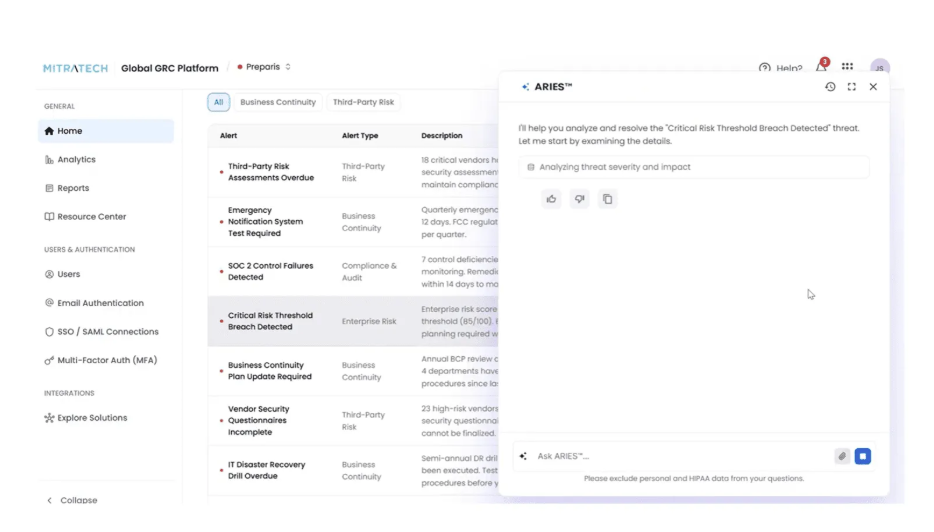
Mitratech is a broader legal, risk, and compliance platform that includes third-party risk management as part of its wider suite. Its TPRM capabilities support structured vendor governance within enterprise environments, including vendor onboarding workflows, risk tiering, due diligence questionnaires, issue tracking, and audit reporting, all integrated with broader legal and compliance processes. A key strength is its alignment with enterprise governance functions. However, the platform is primarily workflow- and governance-driven.
Best for: Enterprises looking to embed TPRM into a wider governance and compliance operating model.
When to avoid it: Avoid it if you want a narrower, security-first vendor risk platform.
Score: 7.2/10
External Risk and Security Ratings Platforms
These platforms provide outside-in visibility into vendor security posture using public data, continuous monitoring, and scoring models. They are useful, but remain abstractions unless paired with a business context.
Key features to look for
- External attack surface monitoring
- Security scoring and benchmarking
- Continuous risk alerts
- Third-party monitoring dashboards
- Breach and vulnerability tracking
9. SecurityScorecard
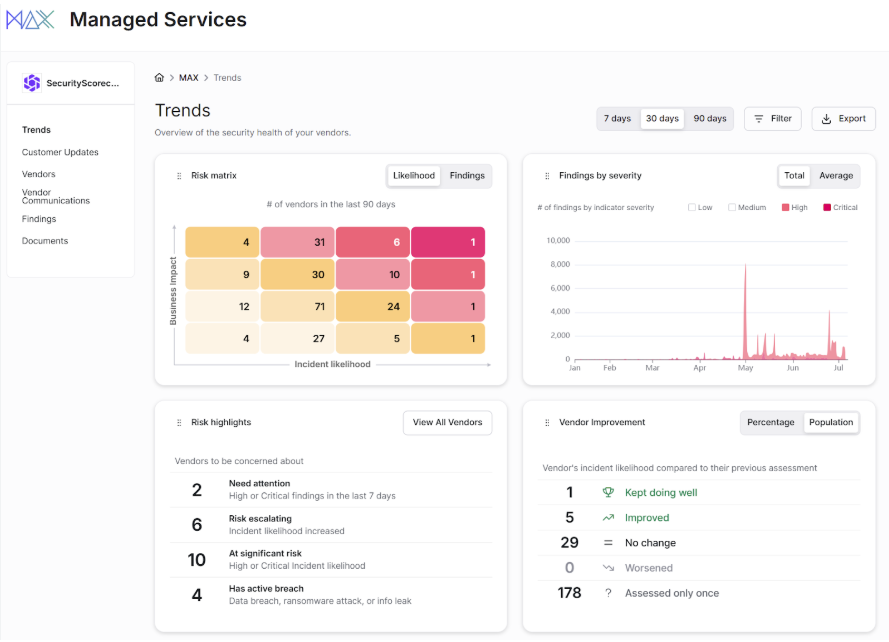
SecurityScorecard is a security ratings platform that provides continuous, outside-in visibility into vendor cyber posture. It analyzes publicly observable signals such as exposed services, vulnerabilities, DNS configurations, patching cadence, and breach indicators to assign each vendor a security score and track changes over time.
Teams can assess and monitor thousands of vendors without requiring questionnaires or direct vendor engagement, making it useful for organizations relying on third-party services across the product development lifecycle, where external dependencies introduce additional attack surface. However, the model is inherently external. Scores are based on observable signals, not on how a vendor is actually used within your environment.
Best for: Teams that want scalable outside-in visibility across large vendor ecosystems.
When to avoid it: Avoid it if you need proof of business impact rather than comparative scores and alerts.
Score: 7.4/10
10. BitSight
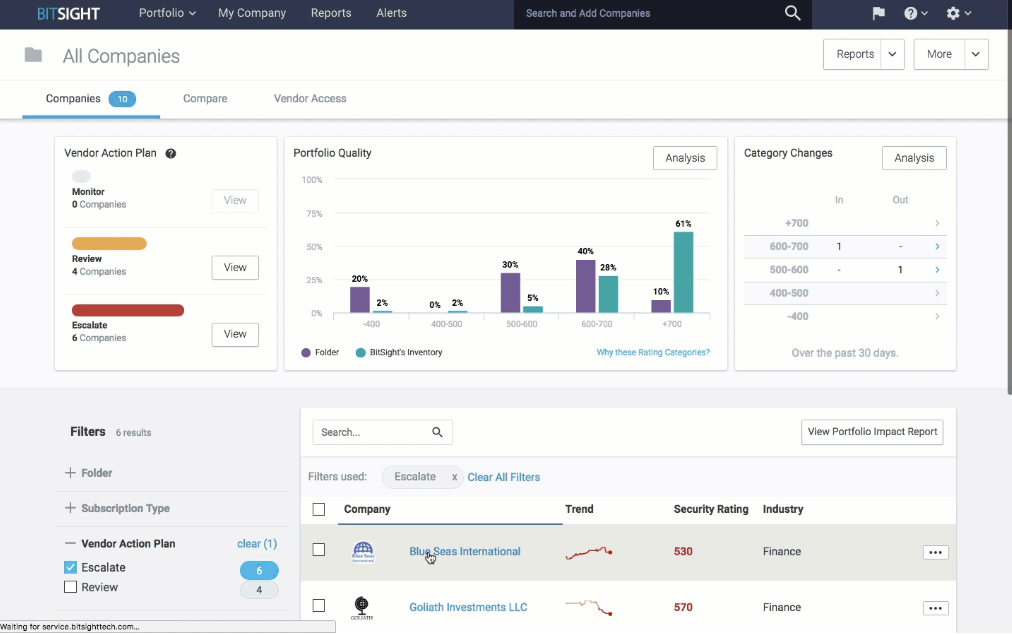
BitSight provides continuous, outside-in visibility into vendor security posture. It analyzes externally observable signals such as network exposure, vulnerabilities, configuration issues, and historical incident data to generate security ratings and track changes over time. It also extends into attack surface intelligence, helping teams identify exposed assets, misconfigurations, and emerging risks across vendor ecosystems.
It’s particularly useful for ongoing monitoring and identifying vendors that may introduce elevated external risk. However, like other security ratings platforms, its perspective is limited to what can be observed externally.
Best for: Organizations that want strong external posture and attack-surface intelligence.
When to avoid it: Avoid it if you need internal relationship context to prioritize risk.
Score: 7.5/10
11. Black Kite
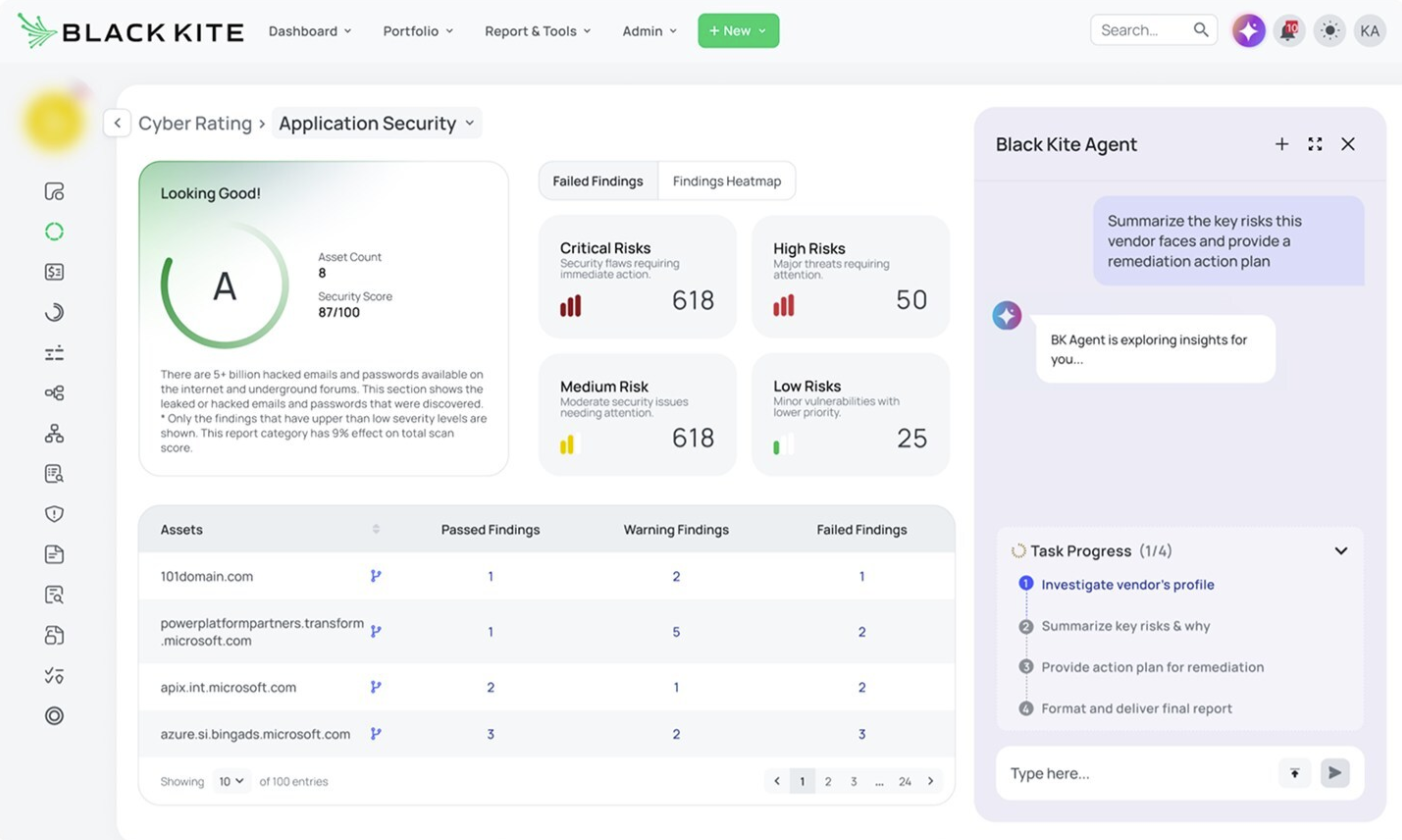
Black Kite goes beyond basic security ratings by layering in threat modeling and financial risk context. It analyzes external signals like vulnerabilities, misconfigurations, breach history, and ransomware exposure, then maps those findings to frameworks such as MITRE ATT&CK and translates them into potential business impact. The result is a more contextual view of how vendor weaknesses can affect your broader perimeter security. That said, it still operates from an outside-in perspective. Insights are based on observable data and modeled scenarios.
Best for: Enterprises that want third-party cyber intelligence with stronger business framing than pure ratings alone.
When to avoid it: Avoid it if your program depends on artifact analysis and internal usage verification.
Score: 7.9/10
IT and Cyber Risk Management Platforms
These tools help organizations quantify, prioritize, and communicate cyber and operational risk, often using financial models and executive reporting.
Key features to look for
- Risk quantification
- Scenario modeling
- Executive reporting in financial terms
- Risk aggregation across domains
- Decision support tools
12. SAFE
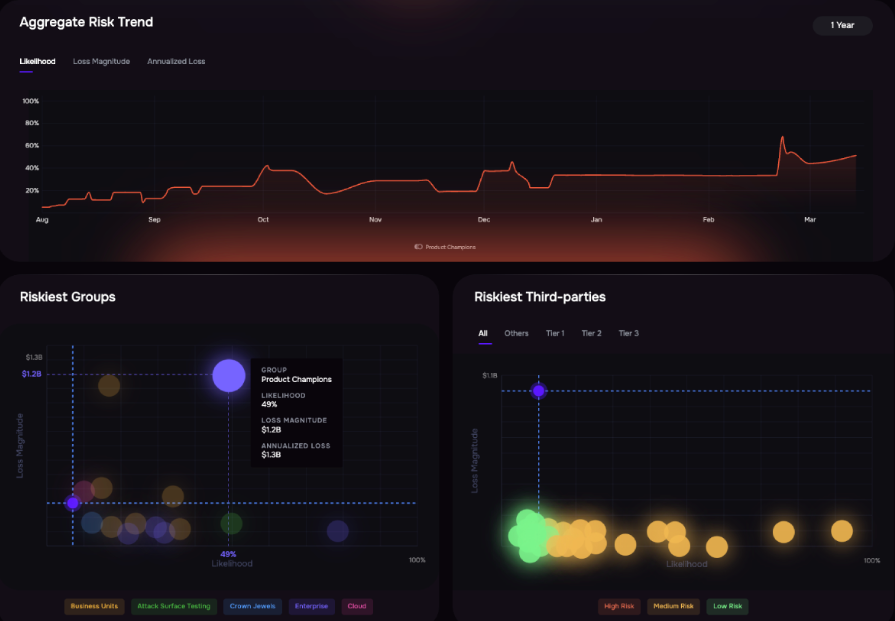
SAFE Security is a cyber risk quantification platform that translates security risks into financial impact. It uses FAIR-based models and scenario analysis to estimate potential losses across enterprise, third-party, and emerging risk areas such as AI. Where it stands out is in decision support. Instead of prioritizing risk based on severity or compliance gaps, SAFE enables teams to quantify exposure in monetary terms, helping security leaders communicate clearly with executives and make risk-informed investment decisions.
Best for: Security leaders who need quantified cyber risk and board-ready decision support.
When to avoid it: Avoid it if your immediate need is workflow-heavy vendor onboarding and assessment operations.
Score: 8.0/10
13. LogicGate
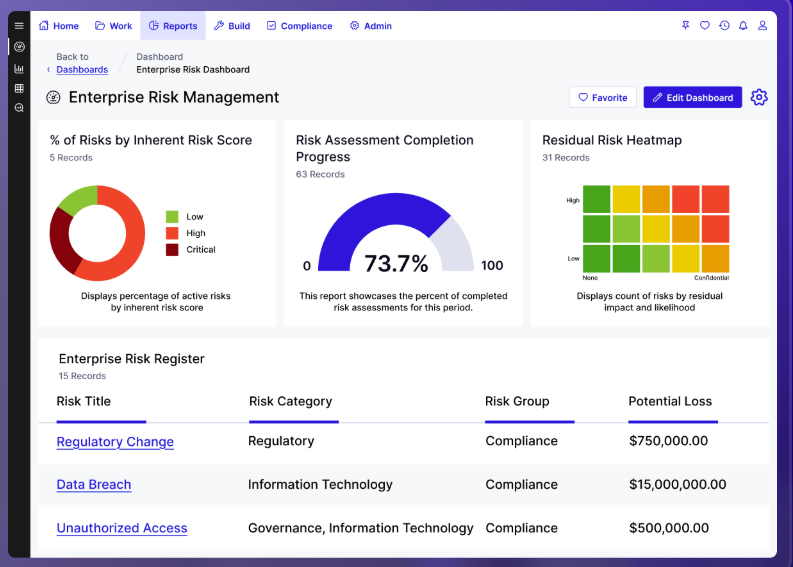
LogicGate is a configurable GRC platform that helps organizations build and automate risk workflows across multiple domains, including cyber risk, compliance, and third-party risk. Its core product, Risk Cloud, allows teams to create custom risk registers, design intake and assessment workflows, automate approvals, and generate reporting tailored to their internal processes. Instead of enforcing a fixed structure, LogicGate lets teams model their own processes all within a single system. This makes it well-suited for organizations that want to consolidate multiple risk and compliance activities into one platform rather than rely on separate tools.
Best for: Organizations that need a highly configurable GRC platform to support multiple risk programs within a single system.
When to avoid it: Avoid it if you want purpose-built depth for a single narrow use case out of the box.
Score: 7.8/10
Choosing the Right GRC Platform for Your Risk Model
GRC is no longer a single category; treating it as one is where most buying decisions go wrong. The platforms in this space solve very different problems, from managing controls and audits to coordinating vendor workflows or monitoring external posture. Each has value, but they operate at different layers of the risk lifecycle. The real question is not which tool is “best,” but which one aligns with how your organization understands and acts on risk.
If your priority is running structured processes, such as managing assessments or tracking controls, many platforms on this list will do so well. But if the goal is to understand where third-party risk actually exists, how it affects your environment, and what needs to be addressed, that requires a different approach.
Lema’s Agentic-AI Risk Engineering platform uncovers and reduces third-party exposure. Instead of relying on questionnaires or static assessments, it analyzes vendor artifacts, gathers external intelligence, and maps how each vendor actually interacts with your environment.
By combining forensic artifact analysis, open-source intelligence, and blast radius mapping, Lema determines whether a vendor poses a real risk to your organization and prioritizes what needs to be fixed. The result is not another workflow or score, but an evidence-backed view of exposure and clear remediation steps.
Book a demo to see the risks that questionnaires, trust centers, and security ratings don’t surface.
FAQs
What Is An Example Of A GRC Tool?
A common example of a GRC (Governance, Risk, and Compliance) tool is a centralized software platform designed to bring together risk management, policy enforcement, and compliance tracking into a single system, helping organizations maintain control and oversight across complex operations.
What Do GRC Tools Do?
GRC tools help organizations identify, assess, and mitigate risks while ensuring adherence to regulatory requirements and internal policies. They streamline processes like audits, reporting, and compliance tracking, often using automation to reduce manual work and provide real-time visibility into risk exposure and governance performance.
Which Is The Best GRC Tool?
The best GRC tool depends on the specific needs and maturity of an organization, but the most effective solutions are those that combine strong automation, clear risk visibility, scalability, and seamless integration with existing systems to support proactive, organization-wide risk and compliance management.


